Ferrum Technology Services Blog
How often do you look at your email solution and think, “Wow, managing this thing takes up so much of our time. What would it be like to take that time and apply it elsewhere?” Today, businesses have all kinds of options for managing their email communications, one of which is email hosting provided through a managed service provider.
Wrangling an email inbox that has been left to its own devices for months can be a challenge, especially for those who sign up for email lists and never unsubscribe from anything. If this sounds like you, be sure to read on and discover ways that you can finally take back control of your email inbox.
As much as we all rely on emails throughout the workday, they can be an intense pain to manage, which only makes it a hassle to deal with and can actively make it less useful for your users. We want to help you avoid this outcome, so we’re sharing a few tips to make the management of your email that much more effective.
Security is always a business priority, and with so many business needs now fulfilled digitally, it is critical that cybersecurity has a strong presence in organizations big and small. Nowadays, collaboration solutions have also had even greater importance in the workplace, making tools like email completely essential. Unfortunately, this gives cybercriminals an increased opportunity to use it as a means of attack.
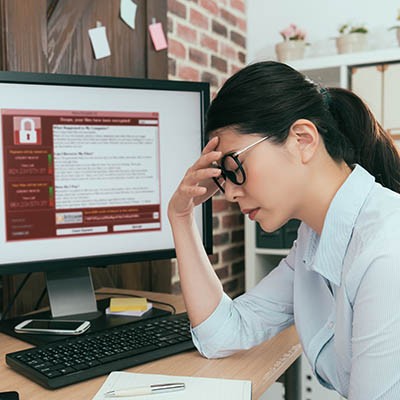
Ransomware has been a real problem for the past several years. This is a result of a shift in the ways hackers approach their craft. Once known for breaching networks directly, the establishment of uncrackable encryption left hackers looking to change their strategies. Today, they use scams to get people to give them access to network resources. If they are successful, it can deliver more than headaches for a business. Let’s look at what makes ransomware so dangerous and how your company can combat the constant attacks that come your way.
With businesses trying to feel out the situation, there is going to be some anxiety, some indecisiveness, even some fear about reopening too early (or too late). It may be a perfect time, however, to start to look at ways you can innovate your business. One way you can do that is by reinventing your business’ communications platform.
Email is a presence in almost every business, but some businesses use it better than others. Some use it as a be-all, end-all business communications solution, while others use it for correspondence that isn’t time sensitive. No matter how your business uses email, managing it properly will go a long way toward improving your efficiency and productivity.
With technologies like machine learning and artificial intelligence entering further into our daily lives, what was once science fiction is becoming fact - assisting our lives (which most would agree is better than threatening our lives). For this week’s tip, we’ll show you how to leverage machine learning in a very basic way: in the Android version of Gmail’s Smart Compose feature.
Ever get an email with the subject line “No Subject” and not feel compelled to open it? Us too. Your email subjects are crucial to getting a user’s attention and helping them understand what the email is about. We’re here to help you develop more effective email subjects to ensure your messages are opened and responded to.
Communication is imperative to the success of your business, but sometimes it’s easier said than done--particularly if your organization relies on technology-related communication that can make context and subtext difficult to detect. Here are some tips to ensure that your employees are as clear and concise as possible with your communication mediums.
The cloud has helped a lot of businesses overcome the boundaries set by the physical workplace. Employees can access data and applications on a variety of devices that were previously thought to be nothing but time-wasters, allowing for an improved workplace experience and much more flexibility. In particular, cloud-based email allows for enhanced connectivity between your organization’s internal and external resources.
If we asked you to identify the biggest risk to your business’ network security, what would you think it would be? Some might think that the countless threats on the Internet are the biggest issues your organization will have to deal with, while others might think natural disasters represent the biggest problem for your business. Many others, however, see the end user as the biggest threat to their business, and they are right… to an extent.
Due to the popularity of email in the business world, it’s an extremely popular method of attack for hackers. They can easily send countless messages to targets all over the world with the click of a mouse. Therefore, you have to take email security very seriously. The repercussions of not doing so could be swift and severe. This week’s tip is dedicated to informing your employees of email best practices for the office environment.
Are your employees putting your organization’s security at risk due to poor email practices? This is a question that all business owners need to consider--especially if you deal in sensitive information. We recommend that all businesses utilize a two-pronged approach to email security, including both technology measures to secure communications on the technical side and training to secure on the human side.
There is a famous thought experiment devised by physicist Erwin Schrӧdinger, describing a very particular paradox in quantum physics through the experience of a cat. While Schrӧdinger’s cat was initially intended to demonstrate a very different phenomenon, it can also be applied to something that all businesses need to consider: their email security.
Email is arguably the most popular method of business correspondence in existence. It’s fast, economical, securable, easy to store/archive, and searchable in a way that traditional, physical records can’t compete with. With billions of emails sent every day from all over the globe, there is a considerable amount of sensitive information transmitted within these communications. The criminal element is looking for every opportunity to steal and exploit personal data, as well as take advantage of vulnerabilities to gain access to a company’s data or network.